Encrypting USB drive: Choose password |
The next step of the wizard lets you choose a password to protect the Virtual Encrypted Disk:
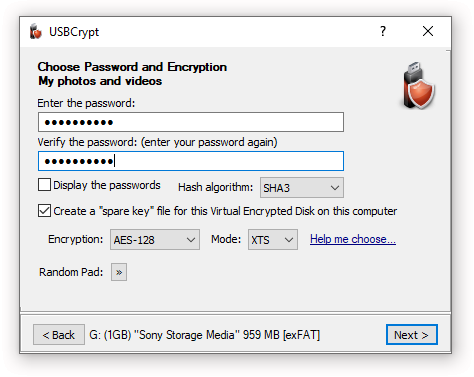
Of course, choosing a good password is tricky. It should be long and complex enough to be hard to guess by others, yet easy enough to remember for you. A strong password should contain a mix of the lower- and -upper-case characters, as well as a few digits and special characters.
Remember that the passwords used by USBCrypt are case-sensitive (that is, Apple, APPLE, and apple are considered different passwords. The maximum number of characters a password may contain is 64.
If you've decided to choose a complex password, you may find the Display password option handy: it lets you see the passwords you are entering in plain view, as they really are. (Just make sure no one is looking over your shoulder before choosing to reveal your password in this way!
Note that if you are still evaluating USBCrypt (that is, you have not purchased a license for its continued use yet), you will see the following warning:
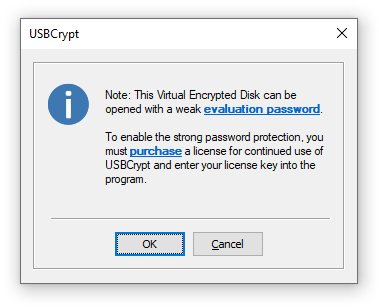
This message reminds you that during the evaluation period USBCrypt is using the "weak" password protection: it allows anyone to recover the "weak" password easily. If you have already purchased a license for the continued use of USBCrypt and entered your license key into the program, then the full, strong password protection will be used and you will not see this message.
Besides choosing the encryption password, you can also select a few related options:
You can choose the hash algorithm to be used to derive the encryption key ![]() from your password. The current choices are:
from your password. The current choices are:
Each of these choices offers comparable security, so it's up to you which one to choose. Keep in mind though that the SHA3 and SHA2 algorithms are only supported in USBCrypt version 18 and later. If you plan on using a version of USBCrypt earlier than 18, then choose the SHA2 Combo algorithm, which is the only hash algorithm supported by the older versions of USBCrypt.
If you select this option the USBCrypt will create a special file on the hard drive of your computer that it can use later on to reset the password of this specific Virtual Encrypted Disk. You should consider carefully whether you want to use this option or not: it may come very handy if you forget your password, but if someone else can get hold of your files on this computer, they would be able to bypass the password protection and access your encrypted files without knowing your password. If you are worried about the latter, you are perfectly free to clear this option, just remember that in such a case if you forget your password, you will lose your encrypted files forever!
Note that you can use USBCrypt to create or erase the "spare key" file after the Virtual Encrypted Disk has been created. Should you change your mind, you can create or delete the "spare key" file later on.
Note also that each Virtual Encrypted Disk you create requires its own "spare key" file: it's impossible to use one "spare key" file to unlock another Virtual Encrypted Disk. Even if you create exactly the same Virtual Encrypted Disk of the same size and protect it with the same password, you should create a new "spare key" file specifically for it: any other "spare key" file would not work.
These options allow you to select the encryption algorithm and encryption mode that should be used for this Virtual Encrypted Disk. AES-128 stands for "Advanced Encryption Standard ![]() with 128-bit key", and AES-256 selects the same AES algorithm but with the 256-bit key.
with 128-bit key", and AES-256 selects the same AES algorithm but with the 256-bit key.
If you have purchased a business license for USBCrypt, you have the option of choosing among several other encryption algorithms: TF-128 stands for Twofish ![]() algorithm with a 128-bit encryption key, and TF-256 means Twofish encryption with a 256-bit key. Finally, the choice of AES-TF-512 gives you the cascade encryption
algorithm with a 128-bit encryption key, and TF-256 means Twofish encryption with a 256-bit key. Finally, the choice of AES-TF-512 gives you the cascade encryption ![]() algorithm that is a combination of AES-256 and TF-256 with the effective key length of 512 bit.
algorithm that is a combination of AES-256 and TF-256 with the effective key length of 512 bit.
The XTS encryption mode ![]() is considered the best choice at the time of this writing. Business customers can also select the CBC mode
is considered the best choice at the time of this writing. Business customers can also select the CBC mode ![]() which is an older standard that has some deficiencies, but may be required for compliance with some requirements you might have. The default selection of AES-128 and XTS should provide the best encryption method for most situations.
which is an older standard that has some deficiencies, but may be required for compliance with some requirements you might have. The default selection of AES-128 and XTS should provide the best encryption method for most situations.
This button opens a small pop-up window that you can use to provide USBCrypt with random data by moving the mouse around that window randomly for a few seconds:
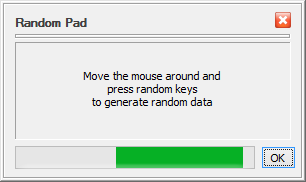
USBCrypt needs random data to generate the encryption keys and related parameters when creating the Virtual Encryption Disk. It collects such random data by monitoring the motion of the mouse and the keystrokes you make while using the previous screens of USBCrypt. Usually it is not necessary to use the Random Pad, because by the time you reach this screen USBCrypt has usually collected enough random data from your use of the previous screens. However, if you want to provide more randomness, you are certainly welcome to use the Random Pad window.
Next step: Formatting the Virtual Encrypted Disk