Encryptability application offers several commands that you can use to change Virtual Encrypted Disks after they've been created.
For example, to change the descriptive name of a Virtual Encrypted Disk, select the Virtual Encrypted Disk in the list, and choose Rename from the File menu. (You can also right-click on the Virtual Encrypted Disk with the mouse and choose Rename from the shortcut menu.) You can rename only one Virtual Encrypted Disk at a time.
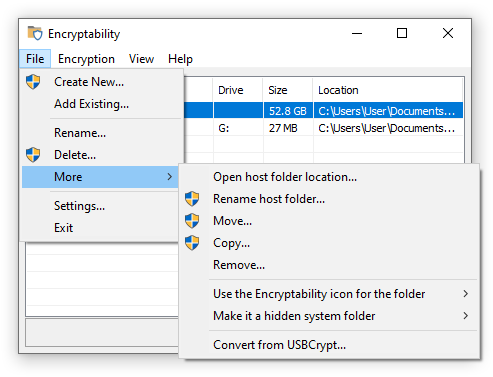
Several other commands for managing the Virtual Encrypted Disks are also available via the More sub-menu of the File menu:
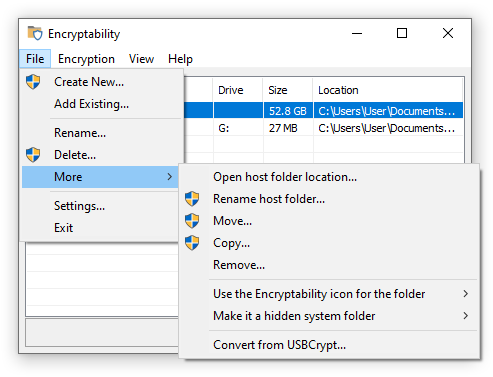
- Open host folder location...
Use this command to open the folder where the Virtual Encrypted Disk files are stored. Keep in mind that you should not rename, move, or otherwise modify any files in that folder, because it may leave the Virtual Encrypted Disk in an inconsistent state and make it inoperable. If you need to perform such actions, use the commands offered by Encryptability, described below.
- Rename host folder...
Use this command to rename the host folder where the Virtual Encrypted Disk files are stored. Remember that this name is not encrypted and may be visible to other users of the computer, when they browse the contents of the storage with File Explorer. You can rename only one host folder at a time. If you want to rename several host folders, select and rename each of them in turn.
- Move...
Use this command to move one or more of the selected host folders of the Virtual Encrypted Disks to another location. This will keep the names of the host folders the same, but move them to a different parent folder of your choosing. If the new parent folder is located on the same physical drive, the moving should take no more than a couple of seconds, but if you are moving the Virtual Encrypted Disks to a different drive, and the size of the Virtual Encrypted Disks is large, it make take a considerable time. After the Virtual Encrypted Disks have been moved, Encryptability will show the new locations in its list.
- Copy...
Use this command to copy one or more of the selected host folders of the Virtual Encrypted Disks to another location. This will create a copy of each selected Virtual Encrypted Disk. If one of the Virtual Encrypted Disks being copied has a spare key, the spare key will be copied as well, to make you able to restore the password of the new Virtual Encrypted Disk, if necessary. After the Virtual Encrypted Disks have been copied, Encryptability will add the new Virtual Encrypted Disks to its list.
NOTE: We do not recommended duplicating Virtual Encrypted Disks in this way, because each copy would get the same encryption key as the original. To avoid that, the proper procedure would be to create a new Virtual Encrypted Disk of the same size (it would get its own encryption key), then start both the original and the new Virtual Encrypted Disks, and copy the encrypted files and folders from the original to the new Virtual Encrypted Disk. (When copying the files this way, they would be automatically decrypted with the original encryption key and then encrypted again with the new encryption key.) If the original Virtual Encrypted Disk is only partially filled, this procedure would also be faster than using the Copy command.
- Remove...
Use this command if you want to remove one or more of the selected Virtual Encrypted Disks from the list maintained by the Encryptability application, without deleting the host folder(s). You can then add the Virtual Encrypted Disks back to the list using the File - Add Existing command. If you want to not only remove the Virtual Encrypted Disks from the list, but also delete the host folders and release the space they occupied for use by other files, use the Delete command instead of the Remove command.
- Resize...
Use this command to resize the selected Virtual Encrypted Disk.
- Use the Encryptability icon for the folder
Use this command to change the images of the host folders for the selected Virtual Encrypted Disks that are displayed when browsing the storage of the computer with File Explorer. Note that you may need to sign off and sign back on to Windows for the change to the icons to take effect.
- Make it a hidden system folder
Use this command to control the visibility of the host folders for the selected Virtual Encrypted Disks in File Explorer. If you turn this option on, then the host folders will not be normally visible, unless the File Explorer option to hide protected operating system files has been turned off by the user. If you turn this option off then the host folders will be visible in File Explorer just like regular folders.
- Convert from USBCrypt...
Use this command to convert a Virtual Encrypted Disk created with USBCrypt software into the format used by Encryptability. After a Virtual Encrypted Disk has been converted, Encryptability will show it in its list.

 Copyright © 2026, WinAbility® Software Corporation
Copyright © 2026, WinAbility® Software Corporation  . All rights reserved
. All rights reserved