Starting the Virtual Encrypted Disk |
When you attach the removable host drive encrypted with USBCrypt to your computer, the USBCrypt icon appears on the "system tray" (officially known as the "taskbar notification area"):
![]()
However, simply attaching the host disk to the computer does not make the encrypted files available for use yet: you need to "start" the Virtual Encrypted Disk first. The easiest way of doing that is via the USBCrypt taskbar icon: simply double-click on it, or right-click and then choose the Start Virtual Encrypted Disk command from the menu:
![]()
If there is no USBCrypt icon on the taskbar, there are other ways of "starting" a Virtual Encrypted Disk. If your computer is configured to automatically run programs from the removable drives when they are plugged it, you may see the following prompt displayed by Windows:

Choose the Open folder to view files command. Or, you can achieve the same result by navigating to the host drive via the Computer (or My Computer) command on Start menu of Windows:
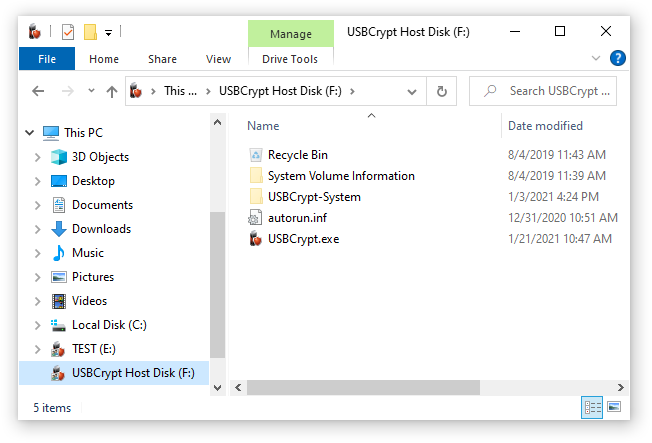
When Windows Explorer window opens, double-click on the USBCrypt.exe file to start USBCrypt software. (You may also see just USBCrypt instead of USBCrypt.exe; if so, double-click on USBCrypt). Also, you may notice a folder named USBCrypt-system there, too: this is a special folder used by USBCrypt to store the files it needs to operate. (Usually this folder is hidden, but your computer may be configured to display the hidden files and folders.) DO NOT go there! OK, I knew it, if told not to do something, it becomes irresistible and now you just have to open that folder, right? OK, go ahead, open it and see what's inside. Nothing interesting, you see? Told you so. Now, close that folder, and don't go there again. OK, if one peek inside was not enough, peek again, but for your own sake, do not delete or rename or do anything else there, because if you do you will void your warranty, lose your encrypted data, and have the eternal curse bestowed upon your entire family. I'm serious. You've been warned. Now get out of the USBCrypt-system folder and never look back.
OK, where were we? USBCrypt should now prompt you to enter your password to start the Virtual Encrypted Disk:
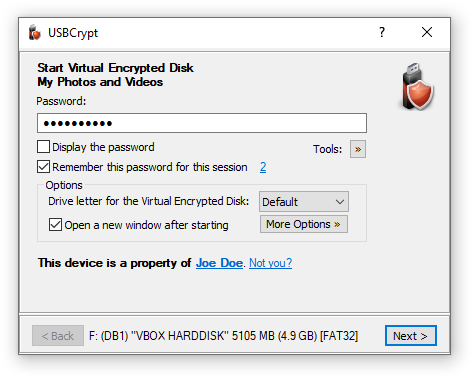
This is the point where those in the know are separated from the rest of the crowd. If you know the password, you will be let in: the Virtual Encrypted Disk will be started and all files and folders it contains will become available for use. If you don't know the password, the Virtual Encrypted Disk will remain the cold pile of useless 1s and 0s and no power in the whole Universe will be able to decrypt them.
Be sure to enter the password exactly as you've supplied it when creating the Virtual Encrypted Disk: the password is case-sensitive, and if you've entered any spaces or special characters when creating the Virtual Encrypted Disk, you need to enter them here as well, in the exact same order. If your computer has several input languages installed, you need to select the correct one, too, by pressing the input language switch key combination defined in Windows Control Panel. You can see the currently selected input language to the right of the password box.
If you are not sure what you've typed in, you can click on the Display the password box and the plain text of the password you've typed in will be displayed in the box. (Before you do that, you may want to check your room for hidden cameras watching your screen. Yes, the bad guys eager to get your secrets could be very sneaky!)
After you have entered the password and before you press the Next button, take a moment to think about the near future: do you plan to disconnect and then attach the same encrypted drive again, before you shut down the computer? Or, do you have another USB drive encrypted with the same password that you plan to start soon, too? If so, you can save yourself a bit of typing and check the box that reads Remember this password for this session. If you check this option then USBCrypt will remember the password you've just entered until your computer is restarted. This ways, if you attach another encrypted drive, you would not need to enter the same password again: when the password prompt for the second drive appears, you can just leave the password box empty and press the Next button. In such a case, USBCrypt would try the passwords that you have chosen to remember and try them to start the second Virtual Encrypted Disk, without you having to enter the same password again.
If you use the Remember this password for this session option, the password will be remembered until you restart Windows, or choose the Forget passwords command, available on the main USBCrypt screen (by clicking on the number that shows the current number the passwords that USBCrypt keeps in the memory. This command is also available on the menu of the USBCrypt taskbar icon, for quick access when you need it.
(In case you are wondering: USBCrypt does not store the plain text of the password, it only stores its hash value. This way, if someone gets hold of your computer and scans its memory looking for the stored passwords, s/he won't find any.)
Note also a few more options on the same window that you can select before pressing the Next button. These options let you control what happens after the Virtual Encrypted Disk is started:
This option lets you choose the drive letter to be assigned to the Virtual Encrypted Disk after it's started. If you select Default, then the next available drive letter will be used. If you want some other specific drive letter to be used, select it in the list.
If you select this option, then USBCrypt will open a new Explorer window to display the contents of the Virtual Encrypted Disk.
You can click this button to open a list of several additional options:
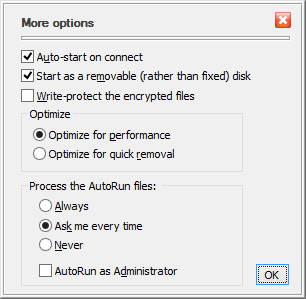
If this option is on, then USBCrypt will automatically display the password entry window when you connect the removable drive to your computer, or when you log in to Windows while the drive is already connected. If this option is off, then you will need to use some other method (like the Start Virtual Encrypted Disk command on the menu of the taskbar icon) to start the Virtual Encrypted Disk off the host drive after you've connected it. Note that this option has effect only if your computer has the USBCrypt software is installed. If you connect the removable disk to some other computer (without USBCrypt software on it), this option has no effect.
When it comes to the auto-play functionality, the Recycle Bin, optimizations, etc., Windows treats the fixed disks slightly differently than the removable ones. If you require the Virtual Encrypted Disk to be treated as a removable disk, select this option.
If you want to protect the contents of the Virtual Encrypted Disk from the accidental (or intentional) changes, select this option: you will still be able to open the files off it and read them but it won't save any changes you make nor will it let you create or delete files or folders on the Virtual Encrypted Disk.
This option allows Windows to use its file cache mechanism when reading from and writing to the Virtual Encrypted Disk. (No, this does not pose a security risk because the cache is used only for the already encrypted data.) This option offers the best possible performance for the Virtual Encrypted Disk. However, it increases the risk of data loss or data corruption, should your computer lose power or crash at a very unfortunate moment.
If you often encounter the situation that you cannot stop the Virtual Encrypted Disk because it's in use by Windows, you may want to select this option. Note however, that it may slow down the data transfer between the Virtual Encrypted Disk and the rest of the system.
You can use this option to control the automatic execution of the AutoRun file off this Virtual Encrypted Disk on this computer.
Of course, you can also leave the options as they are for now, and just enter the password and click Next. What happens then is very much like sort of a digital magic: the random bytes of the Virtual Encrypted Disk that previously were not making sense, are suddenly starting to come together in an orderly way, and the Virtual Encrypted Disk "starts" to come alive: it appears like a regular disk in the Computer folder:
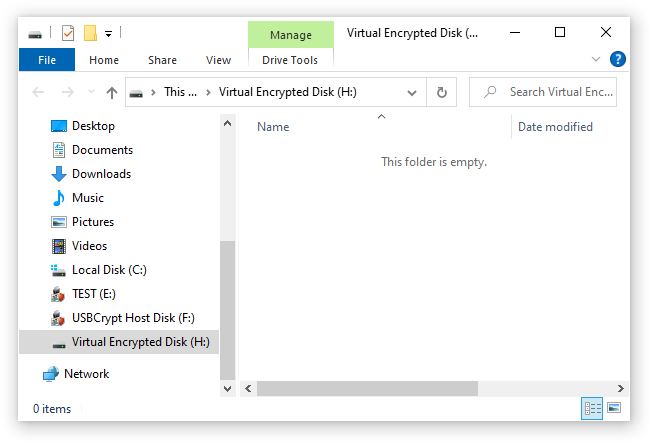
If this is the first time that you've started the Virtual Encrypted Disk, it will be empty. You can start filling it up with the files and folders that you want to be encrypted.
You can see why this disk is called "virtual": there is no actual physical disk with that letter attached to you computer. The C: disk is the main hard drive, the D: disk is your CD-ROM drive, you may or may not have other disks (such as the E: and F: disks shown in the example above). The G: disk is the host USB drive (encrypted with USBCrypt). And, finally, the H: drive, is the virtual disk that appears just like any other disk you might have, but that represents the encrypted area that you have created on the host disk G:.
You can use the Virtual Encrypted Disk just like any real disk: you can create folders inside of it, rename and delete files, change their attributes, open files off it, and so on. You can even defragment the Virtual Encrypted Drive, or share it on your network, if you want. For most practical purposes, the Virtual Encrypted Disk is indistinguishable from any regular disk of the same kind. The only (and very important) difference is that the Virtual Encrypted Disk becomes a disk only after you have entered the correct password. This is something that the regular disks are incapable of.
Go ahead, move your personal files that you want to be encrypted into the Virtual Encrypted Disk that you've just started. If you are only starting learning USBCrypt, you may want not to move, but copy the files for now: in this case, if something goes wrong, and you want to start over, you would still have the original unencrypted copies left on your hard disk. When you are comfortable with the USBCrypt software and the whole concept of the Virtual Encrypted Disks, and also when you have a reliable backup, you can "securely" delete the original unencrypted copies of the private files, and have only the encrypted ones to work with, inside of the Virtual Encrypted Disk.
Now that you've had the Virtual Encrypted Disk started and running, what do you do to lock its back and make the encrypted files protected and inaccessible to no one besides you? For that, you need to stop the Virtual Encrypted Disk and return it to the cold conglomerate of the random 1s and 0s.